Roteamento de entrada/saída com iproute e iptables
Na internet tem muita documentação relacionada com o balanceamento de saída com 2 ou mais links de internet, mas nenhuma documentação relacionada quando você quer ter seus servidores ( email, web, terminal service etc) respondendo para a internet por todos seus links disponíveis.
[ Hits: 45.163 ]
Por: Tiago Henrique Pires em 15/11/2008 | Blog: http://tiagonux.blogspot.com
Introdução
Na internet tem muita documentação relacionada com o balanceamento de saída com 2 ou mais links de internet, mas nenhuma documentação relacionada quando você quer ter seus servidores ( email, web, terminal service etc) respondendo para a internet por todos seus links disponíveis.
Essa solução resolve seu problema da seguinte maneira:
- Sua empresa tem 2 links de internet ou mais;
- Você tem servidores disponibilizando recursos para a internet como smtp, pop3, web, rdp etc;
- Quer que seja transparente para todos quando um link de internet para de funcionar, você pode via DNS round-robin fazer que um host responda por 2 IPs válidos ou mais. Isso seria ótimo para seu servidor de email. São 2 IPs respondendo por smtp e pop3 e caso um link caia o outro fica respondendo normalmente. O DNS é nosso amigo!
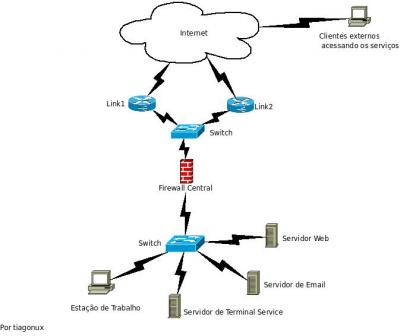
Veja a topologia que iremos nos basear para criar as regras de iptables e iproute: Na topologia acima temos 3 servidores em nossa rede disponibilizando serviços web, pop3, smtp e terminal service à internet.
Na configuração da zona de DNS do domínio utilizamos round-robin para todos os serviços. Cada serviço tem um nome e 2 IPs válidos respondendo por esse nome de DNS.
2. Script de roteamento
Montando um servidor X com o Linux
Firewall/Proxy (solução completa)
Shared Config com Apache a la brasileira
Desvendando as regras de Firewall Linux Iptables
Trabalhando com CARP nos BSD's
Análise da distribuição Mandrake Security
Endian Firewall - Solução completa para um servidor de internet
Automatizando Firewall com IDS Snort e SnortSam
Dúvidas...
1. Como é possível fazer o DNS reverso funcionar com dois links?
2. Neste script você mostra como fazer a priorização de certas portas e diz por qual link tal porta irá sair, mas pelo que vi, esta faltando a divisão de carga entre os links.
Como ficaria por exemplo se caso eu quisesse somar os dois links WAN com a marcação de pacotes?
3. Fazendo a marcação de pacotes em um link muito requisitado, irá ocupar uma maior taxa de processamento? Lentidão?
4. Quem tem mais prioridade, a regra 0 ou a 255?
Parabéns pelo artigo, esta bem explicado.
Olá Tiago, tinha um sistema parecido, porém tive alguns problemas para efetuar este tipo de roteamento.
Acredito que esse artigo me auxiliará bastante a reatar esse sistema com dois links de Internet.
Parabéns e abraços.
Danilo
Olá a todos
Em resposta das dúvidas de downloadd :
1 - O DNS reverso será configurado nos servidores de DNS para cada IP. Você pode ter configurar normalmente em seu servidor caso a operadora de telecom tenha passado isso para você. Ou pedir para as operadoras de Telecom configurar o DNS reverso para cada IP.
2 - O Script não faz priorização de pacotes, o objetivo dele é rotear os pacotes na entrada pelos links. Ele marca o pacote quando ele entrar por um determinado link e assim o pacote voltar pelo link que entrou.
3 - Você pode até fazer um load balance, mas ai ele se encaixa na saída. No script é feito um roteamento mais avançado na entrada do pacote. Você poderá até usar o cbq para criar regras de controle de banda por protocolo ( smtp,pop3) para diminuir a carga de um link.
4 - As regras de roteamento são lidas apartir da prioridade 0. Caso um pacote se encaixe em uma regra de roteamento ele é processado caso não ele vai até o final e poderá ser processado pela ultima regra.
Obrigado a todos que gostaram do artigo, qualquer dúvida estou a disposição.
Muito bom....
Eu já uso o balanceamento de saída para dois links na empresa onde trabalho mas sempre tive este problema para o tráfego de entrada... Ŕealmente é como vc disse, tem muita documentação dizendo como fazer o balanceamento de saída mas não como tratar corretamente o tráfego de entrada...
Seu artigo me ajudou muito...
Parabéns...
[]s
Cloves Jr
Rapaz, achei show este teu artigo. Creio que quem já passou por situação semelhante e não conseguiu resolver, sabe dar real valor ao teu artigo.
Muito show!!!
Alvaro Mendes
caro amigo estou com um modem Gi-Link WL-2404BRG AP-Plus e nao estou conserguido configura ele come e que eu fasso ,para internete vida
Gostei muito... estou adaptando para implementar aqui na empresa...
qualquer dúvida ... sei onde t encontrar...heheh
[]' s
Gostaria de Saber onde foi declarado a variavel LINK_WAN2?
Hahhaha vendo pela figura eu tenho os 2 links em um switch. Assim não é necessário inserir uma outra placa de rede.
Alguém já conseguiu rotear conexões da porta 80, porta 25 para outros servidores usando load bance ?
olá..
preciso de ajuda, para configurar a seguinte regra no meu firewall iptables..
é o seguinte tem um portal dentro da minha rede interna que esta funcionando neste endereço .72.16.1.21 na porta 8080, e quero que ele redirecione para a máquina 182.16.1.2.
quando eu clico no link da pagina onde ele tem que fucionar diz o seguinte este endereço 200.101.122.43:8090 não pode conectar.
como eu faço para poder funcionar na rede interna quando eu clicar no link?
eu fiz a seguinte regra e não funcionou..
iptables -t nat -A PREROUTING -p tcp -s 172.16.1.21 -sport 8080 REDRECT 182.16.1.2:8090
ou
iptables -t nat -A PREROUTING -p tcp -i eth1 -d 200.101.43 -p tcp --dport 8090 -j DNAT --to-destination 182.16.1.2:8090
não sei ja tentei um monte de regras e nenhuma funcionou, será que pode me ajudar.
200.101.122.43- endereço do moldem
172.....- endereço da rede interna
192....-endereço da rede
obrigada pela atenção!
gisele.
Caro
Amigo
Eu estou configurando 2 links em uma maquina firewall ..
e estou usando o seu artigo ..
mas por que não sei ..
não esta funcionando com os dois links só com 1
pode me ajudar
Como está o ambiente seu?? Scritp ?
Lembrando que não é só usar o script de roteamento as regras de firewall também devem estar preparadas para o ambiente.
Ok
Ai vai o meu script de firewall
#!/bin/bash
IPTABLES=`which iptables`
# -----------------------
PME="eth0"
GVT="eth1"
VPN="tun0"
# -----------------------
VLAN_SOFT=10.1.x.0/24
VLAN_TELEFONIA=10.10.2.0/26
# -----------------------
PME_GW="201.x.x.xx"
GVT_GW="200.xx.xx.xx"
# -----------------------
LINK_PME="eth0"
LINK_GVT="eth1"
REDE_INT="eth3"
# -----------------------
IP_PME="201.x.x.h"
IP_GVT="200.x.x.y"
# -----------------------
MAIL_PORT=22,25,80,110
WWW_PORT=80,81,82,443,1533
WWW_PORT0=8008,8080,8081,8082
# -----------------------
case $1 in
start)
echo "|=====================================================|"
echo "|:Script de Firewall - IPTABLES |"
echo "|:Criado por: Eduardo Gomes |"
echo "|:Técnico em Informática |"
echo "|:suportlinux@yahoo.com.br |"
echo "|:Uso: /etc/init.d/firewall |"
echo "|:$HOSTNAME:.............................ok:|"
echo "|=====================================================|"
echo "|:LIMPANDO AS REGRAS DO FIREWALL:..................ok:|"
$IPTABLES -F
$IPTABLES -Z
$IPTABLES -X
$IPTABLES -F -t nat
$IPTABLES -X -t nat
$IPTABLES -F -t mangle
$IPTABLES -X -t mangle
$IPTABLES -Z -t mangle
$IPTABLES -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
echo "|:Create Reject-and-log-SSH-Bruteforce:............ok:|"
$IPTABLES -N REJECT-SSH
$IPTABLES -A REJECT-SSH -j DROP -m recent --rcheck --name SSH --seconds 60 --hitcount 10
$IPTABLES -A REJECT-SSH -j LOG --log-prefix SSH-Bruteforce:
$IPTABLES -A REJECT-SSH -j REJECT -p tcp --reject-with tcp-reset
$IPTABLES -A REJECT-SSH -j REJECT
echo "|:Blacklist SSH:...................................ok:|"
$IPTABLES -N ssh
$IPTABLES -N blacklist
$IPTABLES -A blacklist -m recent --name blacklist --set
$IPTABLES -A blacklist -j LOG --log-prefix 'SSH REJECTED: '
$IPTABLES -A blacklist -j REJECT
# ------------------------------------------------------------
# echo "|:Inclua aqui teus ips para não sofrer o bloqueio:.ok:|"
# $IPTABLES -A ssh -i eth1 -s 10.10.10.13/32 -p tcp --dport 22 -j ACCEPT
# ------------------------------------------------------------
$IPTABLES -A ssh -m recent --set --name couting1
$IPTABLES -A ssh -m recent --update --name couting1 --seconds 20 --hitcount 3 -j blacklist
$IPTABLES -A ssh -j ACCEPT
echo "|:Kill SSH Brute-force attacks:....................ok:|"
$IPTABLES -A INPUT -p tcp --dport 22 -m state --state NEW -m recent --update --name SSH --seconds 60 --hitcount 4 -j REJECT-SSH
$IPTABLES -A INPUT -p tcp --dport 22 -m state --state NEW -m recent --set --name SSH
echo "|:Liberar as portas principais do servidor:........ok:|"
$IPTABLES -A INPUT -p tcp --dport 22 -j ACCEPT
$IPTABLES -A INPUT -p tcp --dport 25 -j ACCEPT
$IPTABLES -A INPUT -p tcp --dport 53 -j ACCEPT
$IPTABLES -A INPUT -p udp --dport 53 -j ACCEPT
$IPTABLES -A INPUT -p tcp --dport 80 -j ACCEPT
$IPTABLES -A INPUT -p udp --dport 1571 -j ACCEPT
$IPTABLES -A INPUT -p tcp --dport 1723 -j ACCEPT
$IPTABLES -A INPUT -p udp --dport 5060 -j ACCEPT
$IPTABLES -A INPUT -p tcp --dport 9998 -j ACCEPT
$IPTABLES -A INPUT -p udp --dport 10000:20000 -j ACCEPT
$IPTABLES -A INPUT -p tcp --dport 10024 -j ACCEPT
$IPTABLES -A INPUT -p tcp --dport 10025 -j ACCEPT
echo "|:REGRAS DE INPUT:.................................ok:|"
$IPTABLES -A INPUT -p icmp -s 10.10.1.0/27 -d 0/0 -j ACCEPT
$IPTABLES -A INPUT -p icmp -s 10.10.2.0/26 -d 0/0 -j ACCEPT
$IPTABLES -A INPUT -p icmp -s 10.10.3.0/25 -d 0/0 -j ACCEPT
$IPTABLES -A INPUT -p icmp -s 10.10.7.0/25 -d 0/0 -j ACCEPT
$IPTABLES -A INPUT -p icmp -s 10.10.10.0/24 -d 0/0 -j ACCEPT
$IPTABLES -A INPUT -p icmp -s 10.20.20.0/24 -d 0/0 -j ACCEPT
$IPTABLES -A INPUT -p tcp --syn -s 10.10.1.0/27 --dport 3128 -j ACCEPT
$IPTABLES -A INPUT -p tcp --syn -s 10.10.2.0/26 --dport 3128 -j ACCEPT
$IPTABLES -A INPUT -p icmp -j DROP
$IPTABLES -A INPUT -j LOG --log-prefix "INPUT Barrado: "
$IPTABLES -A INPUT -j REJECT
$IPTABLES -P INPUT DROP
echo "|:REGRAS DE PREROUTING E REDIRECIONAMENTO:.........ok:|"
echo "|:..........************* QoS *************........ok:|"
$IPTABLES -t mangle -A POSTROUTING -p udp --sport 1571 -j TOS --set-tos 16
$IPTABLES -t mangle -A POSTROUTING -p udp --sport 5060 -j TOS --set-tos 16
$IPTABLES -t mangle -A POSTROUTING -p udp --sport 5061 -j TOS --set-tos 16
$IPTABLES -t mangle -A POSTROUTING -p udp --sport 10000:20000 -j TOS --set-tos 16
$IPTABLES -t mangle -A PREROUTING -p udp --dport 1571 -j TOS --set-tos 16
$IPTABLES -t mangle -A PREROUTING -p udp --dport 5060 -j TOS --set-tos 16
$IPTABLES -t mangle -A PREROUTING -p udp --dport 5061 -j TOS --set-tos 16
$IPTABLES -t mangle -A PREROUTING -p udp --dport 10000:20000 -j TOS --set-tos 16
# echo "|:..........************* HTB *************........ok:|"
# $IPTABLES -t mangle -A POSTROUTING -p udp --sport 10000:20000 -j MARK --set-mark 0x10
# $IPTABLES -t mangle -A POSTROUTING -p udp --sport 5060 -j MARK --set-mark 0x10
# $IPTABLES -t mangle -A PREROUTING -p udp --dport 10000:20000 -j MARK --set-mark 0x10
# $IPTABLES -t mangle -A PREROUTING -p udp --dport 5060 -j MARK --set-mark 0x10
#$IPTABLES -t nat -A PREROUTING -p tcp --dport 80 -i eth0 -j DNAT --to 10.10.2.4
#$IPTABLES -t nat -A PREROUTING -p tcp --dport 80 -i eth1 -j DNAT --to 10.10.2.4
# $IPTABLES -t nat -A PREROUTING -p udp --dport 5060:5080 -i eth0 -j DNAT --to 10.10.2.4
# $IPTABLES -t nat -A PREROUTING -p udp --dport 5060:5080 -i eth1 -j DNAT --to 10.10.2.4
# $IPTABLES -t nat -A PREROUTING -p udp --dport 10000:20000 -i eth0 -j DNAT --to 10.10.2.4
# $IPTABLES -t nat -A PREROUTING -p udp --dport 10000:20000 -i eth1 -j DNAT --to 10.10.2.4
# echo "|:Proxy transparente para toda as redes:...........ok:|"
# $IPTABLES -A PREROUTING -t nat -p tcp -s $TELEFONIA --dport 80 -j REDIRECT --to-port 3128
# $IPTABLES -A PREROUTING -t nat -p tcp -s $SOFT --dport 80 -j REDIRECT --to-port 3128
echo "|:Marcar pacotes para usar o Link 1:...............ok:|"
$IPTABLES -t mangle -A PREROUTING -i eth0 -p tcp --dport 80 -d $IP_PME -m conntrack --ctorigdst $IP_PME -j MARK --set-mark 1 -m mark --mark 0
echo "|:Marcar pacotes para usar o Link 2:...............ok:|"
$IPTABLES -t mangle -A PREROUTING -i eth1 -p tcp --dport 80 -d $IP_GVT -m conntrack --ctorigdst $IP_GVT -j MARK --set-mark 2 -m mark --mark 0
$IPTABLES -t mangle -A PREROUTING -i eth0 -j CONNMARK --save-mark
$IPTABLES -t mangle -A PREROUTING -i eth1 -j CONNMARK --save-mark
$IPTABLES -t mangle -A PREROUTING -i eth3 -p tcp -m state --state ESTABLISHED,RELATED -j CONNMARK --restore-mark
echo "|:................................:...........ok:|"
# echo "|:Proxy transparente para toda as redes:...........ok:|"
# ip route del default
# echo "|:................................:...........ok:|"
# ip rule del prio 10 table main
# ip rule del prio 19 fwmark 1 from 192.168.1.3 table link1
# ip rule del prio 20 fwmark 2 from 192.168.1.3 table link2
# ip rule del prio 21 fwmark 3 from 192.168.1.3 table link1
# ip rule del prio 22 fwmark 4 from 192.168.1.3 table link2
# ip rule del prio 23 fwmark 5 from 192.168.1.2 table link1
# ip rule del prio 24 fwmark 6 from 192.168.1.2 table link2
# ip rule del prio 25 fwmark 7 from 192.168.1.4 table link1
# ip rule del prio 26 fwmark 8 from 192.168.1.4 table link2
ip rule add prio 30 table link1
# echo "|:Configurando as tabelas de cada Link:............ok:|"
if ! cat /etc/iproute2/rt_tables | grep -q '^250'
then
echo "250 link1" >> /etc/iproute2/rt_tables
fi
#
if ! cat /etc/iproute2/rt_tables | grep -q '^251'
then
echo "251 link2" >> /etc/iproute2/rt_tables
fi
echo "|:Flush nas tabelas:...............................ok:|"
ip route flush table link1
ip route flush table link2
echo "|:Falo que prioridade a tabela main tem:...........ok:|"
# ip rule add prio 10 table main
echo "|:Falo quem é o gateway da tabela link1:...........ok:|"
ip route add default proto static via $PME_GW src $IP_PME table link1
echo "|:Falo quem é o gateway da tabela link2:...........ok:|"
ip route add default proto static via $GVT_GW src $IP_GVT table link2
# Crio a regra de roteamento para cada tabela de acordo com a marcação do pacote
echo "|:Pacotes http que entraram pela tabela link1:.....ok:|"
ip rule add fwmark 1 from 10.10.2.4 table link1 prio 19
echo "|:Pacotes http que entraram pela tabela link2:.....ok:|"
ip rule add fwmark 2 from 10.10.2.4 table link2 prio 20
# pacotes pop3 que entraram pela tabela link1
#ip rule add fwmark 3 from 192.168.1.3 table link1 prio 21
#ip rule add prio 30 table link1
ip route flush cache
echo "|:ATIVA O MASCARAMENTO DE SAÍDA:...................ok:|"
$IPTABLES -t nat -A POSTROUTING -o eth0 -j MASQUERADE
$IPTABLES -t nat -A POSTROUTING -o eth1 -j MASQUERADE
echo "|:ATIVAR O REDIRECIONAMENTO NO ARQUIVO IP_FORWARD:.ok:|"
echo "1" > /proc/sys/net/ipv4/ip_forward
echo "1" > /proc/sys/net/ipv4/icmp_echo_ignore_broadcasts
echo "|:REGRAS DE FORWARD:...............................ok:|"
$IPTABLES -A FORWARD -m state --state ESTABLISHED,RELATED -j ACCEPT
$IPTABLES -A FORWARD -p tcp ! --syn -m state --state NEW -j DROP
$IPTABLES -A FORWARD -m state --state INVALID -j DROP
echo "|:IPS COM PRIVILEGIOS ESPECIAIS:...................ok:|"
$IPTABLES -A FORWARD -s 10.10.2.4/32 -j ACCEPT
$IPTABLES -A FORWARD -s 10.10.2.5/32 -j ACCEPT
echo "|:Liberar portas de saída:.........................ok:|"
$IPTABLES -A FORWARD -p tcp --dport 21 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 21 --sport 1024:65535 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 22 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 22 --sport 1024:65535 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 25 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 25 --sport 1024:65535 -j ACCEPT
$IPTABLES -A FORWARD -p udp --dport 53 -j ACCEPT
$IPTABLES -A FORWARD -p udp --dport 53 --sport 1024:65535 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 80 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 80 --sport 1024:65535 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 443 -j ACCEPT
$IPTABLES -A FORWARD -p tcp --dport 443 --sport 1024:65535 -j ACCEPT
$IPTABLES -A FORWARD -p udp --dport 5060 -j ACCEPT
$IPTABLES -A FORWARD -p udp --dport 5060 --sport 1024:65535 -j ACCEPT
#$IPTABLES -A FORWARD -j LOG --log-prefix "FORWARD Barrado: "
#$IPTABLES -A FORWARD -j REJECT
$IPTABLES -P FORWARD ACCEPT
echo "|:REGRAS DE OUTPUT:................................ok:|"
$IPTABLES -A OUTPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
echo "|:..........************* QoS *************........ok:|"
$IPTABLES -t mangle -A OUTPUT -p udp --dport 1571 -j TOS --set-tos 16
$IPTABLES -t mangle -A OUTPUT -p udp --dport 5060 -j TOS --set-tos 16
$IPTABLES -t mangle -A OUTPUT -p udp --dport 5061 -j TOS --set-tos 16
$IPTABLES -t mangle -A OUTPUT -p udp --dport 10000:20000 -j TOS --set-tos 16
$IPTABLES -t mangle -A OUTPUT -p udp --dport 1571 -j TOS --set-tos 16
$IPTABLES -t mangle -A OUTPUT -p udp --dport 5060 -j TOS --set-tos 16
$IPTABLES -t mangle -A OUTPUT -p udp --dport 5061 -j TOS --set-tos 16
$IPTABLES -t mangle -A OUTPUT -p udp --dport 10000:20000 -j TOS --set-tos 16
$IPTABLES -P OUTPUT ACCEPT
;;
stop)
$IPTABLES -F
$IPTABLES -Z
$IPTABLES -X
$IPTABLES -F -t nat
$IPTABLES -X -t nat
$IPTABLES -F -t mangle
$IPTABLES -X -t mangle
$IPTABLES -P INPUT ACCEPT
$IPTABLES -P FORWARD ACCEPT
;;
stats)
$IPTABLES -nL
;;
restart)
$0 stop
$0 start
;;
nat)
$IPTABLES -L -v -t nat -n
;;
mangle)
$IPTABLES -t mangle -L
;;
*)
echo "Usage: $0 [start|stop|stats|restart|nat|mangle]"
;;
esac
Oi
Tiago
Você pode me ....
ajudar........
E ai cara,
seguinte as suas regras ofuscaram minha visão rsrsrrss, brincadeira
veja se isso lhe ajuda http://tiagonux.blogspot.com/2008/12/iproute-avanado.html
como cada um tem suas próprias regras de firewall fica dificil te falar sem eu pode executar suas regras em um ambiente com 2 links.
Tente ver o link e de um retorno....
Bom
Dia
Tiago
Ainda estou com problemas.....
Sera que é pedir d+ um simples script....
só quero poder se conectar com o porta 80 e 22 em ambos os ips....
o meu E-mail esilva@soft.com.br, suportlinux@yahoo.com.br
Fone 21 3527-0293 21 8112-3463
Boa Noite!!!
Problema Urgente com roteamento de Links.
Possuo na empresa, 3 Links,
Link 1 - 10.1.1.1
Link 2 - 10.1.1.2
Link 3 - 10.1.1.3
Ampos são ADSL empresarias, da OI, os modens estão em modo Router, os 3 modens estão conectados em um Switch de 8 portas 3com, e no servidor Linux Debian.
Informações do Servidor
eth0 - Links - 10.1.1.30
eth1 - Local - 192.168.1.1
Preciso que o link 10.1.1.1 seja usado normalmente para navegação, ja esta perfeito.
E tenho na rede um servidor 2003server com ip 192.168.1.253, que é utilizado para wts externo, gostaria de fazer com que este servidor usasse os links 2 e Link 3.
Eu iria distribuir para os usuários o IP válido do Link2 e Link3, os usuarios vão conectar em ambos os links, uma parte em um link e outra parte em outro link. Só que não sei como faço o redirecionamento no servidor, pois tenho uma placa de rede para os 3 links...
Alguem tem alguma solução? Sem que precise colocar mais 2 placas de rede?
Estou precisando disso urgente!
Amigo, tenho 3 links funcionando em meu servidor, uso o fedora core 7, e tenho apenas 2 placas de rede, segue meu script, talvez possa te ajudar, qualquer coisa posta aqui.
#!/bin/sh
## limpeza das regras iptables
iptables -F -t nat
iptables -Z -t nat
iptables -F -t mangle
iptables -Z -t mangle
iptables -X -t mangle
iptables -t mangle -F
iptables -F INPUT
iptables -F OUTPUT
iptables -F FORWARD
iptables -X -t nat
iptables -F
iptables -X
iptables -P INPUT ACCEPT
iptables -P OUTPUT ACCEPT
iptables -P FORWARD ACCEPT
## Configurado é uma unica placa de rede 3 ips diferentes ou seja 3 redes
## basta configurar nas maquinas dos usuarios os ips no qual queira que eles passe pelo link x
## link Default: 175.200.2.1
## link 2: 173.200.2.1
## link 3: 174.200.2.1
############# LINK2 ///// os ips abaixo do eth0 é o gateway do modem
ip route del default dev eth0 via 189.59.13.12 table link2
ip route add default dev eth0 via 189.59.13.12 table link2
#
iptables -t mangle -D PREROUTING -i eth1 -s 173.200.2.0/24 -p tcp -j MARK --set-mark 1
iptables -t mangle -A PREROUTING -i eth1 -s 173.200.2.0/24 -p tcp -j MARK --set-mark 1
ip rule del from 173.200.2.0/24 lookup link2
ip rule add from 173.200.2.0/24 lookup link2
############# LINK3 ///// os ips abaixo do eth0 é o gateway do modem
ip route del default dev eth0 via 187.58.56.111 table link3
ip route add default dev eth0 via 187.58.56.111 table link3
#
iptables -t mangle -D PREROUTING -i eth1 -s 174.200.2.0/24 -p tcp -j MARK --set-mark 2
iptables -t mangle -A PREROUTING -i eth1 -s 174.200.2.0/24 -p tcp -j MARK --set-mark 2
ip rule del from 174.200.2.0/24 lookup link3
ip rule add from 174.200.2.0/24 lookup link3
#
ip route flush cached
iptables -t nat -A POSTROUTING -s 175.200.2.0/24 -j MASQUERADE
iptables -t nat -A POSTROUTING -s 173.200.2.0/24 -j MASQUERADE
iptables -t nat -A POSTROUTING -s 174.200.2.0/24 -j MASQUERADE
iptables -t nat -A PREROUTING -s 175.200.2.0/24 -p tcp --dport 80 -j REDIRECT --to-port 3128
#deve adicionar na tabela do iproute as variaveis dos links
#uso o fedora 7 /etc/iproute2/rt_tables
#adicione as seguintes linhas vi /etc/iproute2/rt_tables
35 link2
36 link3
para testar vá em uma maquina do usuario, configure os ips em qual link que você queira que
ele pertença e vá o prompt de comando e digite tracert -d 8.8.8.8 e ele vai mostrar pelo qual link
sua navegação está saindo.
Tiago,
Estou tentando adaptar seu script para minha necessidade e fiquei com duvida aqui nestas linhas:
# Falo quem é o gateway da tabela link2
ip route add default proto static via $LINK2_GW src $LINK1_IP table link2
É assim mesmo ou deveria ser:
# Falo quem é o gateway da tabela link2
ip route add default proto static via $LINK2_GW src $LINK2_IP table link2
Alterei o IP do link2: $LINK2_IP table link2
Grato pela atencao
Mmoreira
Está correta da sua forma,
ip route add default proto static via $LINK2_GW src $LINK2_IP table link2
Vlw
tiago
Estou tentando usar seu script para fazer exatamente o que voce fez no exemplo, rotear algumas portas usando 2 links de internet. Fiz as devidas modificacoes no scritp mas nao esta funcionando. Um detalhe é que nao tenho nenhuma regra ainda de firewall definida, apenas o seu script esta sendo executado, formatei uma maquina, instalei o debian lenny e executo o script abaixo. repare que fiz poucas modificacoes, basicamente adicionei os meus enderecos ip e gateway:
#!/bin/bash
# Por tiagonux
# Script que faz um servidor GNU/Linux com mais de um link de internet
# rotear os pacotes destinados a sua DMZ. Sua DMZ ficaráespondendo
# a partir da internet pela quantidade de links que tiver.
# Envolve os softwares iproute e iptables
# O script nãcobre regras de mascaramento de pacotes e nem redirecionamento
# de portas.
# Esse script pode ser chamado pelo script de firewall atual do seu sistema, sendo
# que as regras da tabela mangle sãresetadas.
# Variáis
#
# Gateways de cada link
LINK1_GW="xxx.115.xxx.x1"
LINK2_GW="2xx.1x.xxx.x"
#
# Interface de rede ligada aos links e interface ligada a DMZ e rede interna
#
LINK_WAN1="eth1"
LINK_WAN2="eth2"
LINK_INT1="eth0"
#
# IPs de cada Link. Lembrando que se estiver usando apenas uma placa de rede conectada
# em um switch que tem os 2 links (ou mais) deve-se configurar os IPs vádos
# virtualmente na mesma placa de rede.
#
LINK1_IP="xx7.xxx.xx0.xx"
LINK2_IP="xx1.x7.xx0.x0"
#
IPTABLES=`which iptables`
#
# Vocêode chamar esse script de dentro do seu script de firewall atual, mas fazendo
# as devidas alteraçs de redirecionamento de portas.
# Regras de marcaç de pacotes com iptables e seu móo CONNMARK
#
# Reseto tudo da tabela Mangle
$IPTABLES -t mangle -F
$IPTABLES -t mangle -X
$IPTABLES -t mangle -Z
#
# Vocêeve ter um redirecionamento de portas para cada pacote entrando em cada link
# para seu servidor especÃco.
# Aqui marco o pacote que entra pelo link1 com o mark 1 com destino ao IP do LINK1_IP
# e a porta 25 .
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN1 -p tcp --dport 25 -d $LINK1_IP -m conntrack --ctorigdst $LINK1_IP -j MARK --set-mark 1 -m mark --mark 0
#
# Aqui marco o pacote que entrar pelo link2 com mark 2 com destino ao IP do LINK2_IP
# e a porta 25
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN2 -p tcp --dport 25 -d $LINK2_IP -m conntrack --ctorigdst $LINK2_IP -j MARK --set-mark 2 -m mark --mark 0
#
# Aqui marco o pacote que entrar pelo link1 com mark 3 com destino ao IP do LINK1_IP
# e a porta 110 .
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN1 -p tcp --dport 110 -d $LINK1_IP -m conntrack --ctorigdst $LINK1_IP -j MARK --set-mark 3 -m mark --mark 0
#
# Aqui marco o pacote que entrar pelo link2 com mark 4 com destino ao IP do LINK2_IP
# e a porta 110
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN1 -p tcp --dport 110 -d $LINK2_IP -m conntrack --ctorigdst $LINK2_IP -j MARK --set-mark 4 -m mark --mark 0
#
# Aqui marco o pacote que entrar pelo link1 com mark 5 com destino ao IP do LINK1_IP
# e a porta 80
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN1 -p tcp --dport 80 -d $LINK1_IP -m conntrack --ctorigdst $LINK1_IP -j MARK --set-mark 5 -m mark --mark 0
#
# Aqui marco o pacote que entrar pelo link2 com mark 6 com destino ao IP do LINK2_IP
# e a porta 80
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN2 -p tcp --dport 80 -d $LINK2_IP -m conntrack --ctorigdst $LINK2_IP -j MARK --set-mark 6 -m mark --mark 0
#
# Aqui marco o pacote que entrar pelo link1 com mark 7 com destino ao IP do LINK1_IP
# e a porta 3389
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN1 -p tcp --dport 3389 -d $LINK1_IP -m conntrack --ctorigdst $LINK1_IP -j MARK --set-mark 7 -m mark --mark 0
#
# Aqui marco o pacote que entrar pelo link2 com mark 8 com destino ao IP do LINK2_IP
# e a porta 3389
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN1 -p tcp --dport 3389 -d $LINK2_IP -m conntrack --ctorigdst $LINK2_IP -j MARK --set-mark 8 -m mark --mark 0
#
# Aqui énde acontece a máca. Quando simplesmente marcamos um pacote que entra
# por um link de internet ele perde sua marca quando passa pela tabela NAT. Ãnesse
# ponto que todo mundo fica perdido, pois em todos os fós que li a dú maior é# essa, o porque do pacote nãretorna pelo link que ele entrou se eu marquei ele na
# sua entrada.
#
# Acontece que ao passar de uma tabela (mangle) para outra (nat) ele perde a marca.
# Descobri isso lendo a documentaç do iptables e com ajuda do tcpdump concluÃsso.
# Mas sempre tem uma maneira de resolver esse problema.
# Simplesmente vamos dizer que queremos que seja lembrado a marca anterior do
# pacote.
# Como pode ser visto na regra abaixo, na chain PREROUTING da mangle salvo a marca
# do pacote jogando para o ALVO CONNMARK
#
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN1 -j CONNMARK --save-mark
$IPTABLES -t mangle -A PREROUTING -i $LINK_WAN2 -j CONNMARK --save-mark
#
# E quando o pacote retorna entrando pela interface interna éembrado sua marca
# anterior.
# Isso tudo ocorre pela --save-mark da regra anterior e --restore-mark da regra abaixo.
#
$IPTABLES -t mangle -A PREROUTING -i $LINK_INT1 -p tcp -m state --state ESTABLISHED,RELATED -j CONNMARK --restore-mark
#
# Regras de roteamento com iproute
#
# Deletando as regras atuais de roteamento
#
ip route del default
ip rule del prio 10 table main
ip rule del prio 19 fwmark 1 table link1
ip rule del prio 20 fwmark 2 table link2
ip rule del prio 21 fwmark 3 table link1
ip rule del prio 22 fwmark 4 table link2
ip rule del prio 23 fwmark 5 table link1
ip rule del prio 24 fwmark 6 table link2
ip rule del prio 25 fwmark 7 table link1
ip rule del prio 26 fwmark 8 table link2
ip rule add prio 30 table link1
#
# Configurando se necessáo o /etc/iproute2/rt_tables com as tabelas de cada link.
#
if ! cat /etc/iproute2/rt_tables | grep -q '^250'
then
echo "250 link1" >> /etc/iproute2/rt_tables
fi
#
if ! cat /etc/iproute2/rt_tables | grep -q '^251'
then
echo "251 link2" >> /etc/iproute2/rt_tables
fi
#
# Flush nas tabelas
ip route flush table link1
ip route flush table link2
#
# Falo que prioridade a tabela main tem.
ip rule add prio 10 table main
#
# Falo quem é gateway da tabela link1
ip route add default proto static via $LINK1_GW src $LINK1_IP table link1
#
# Falo quem é gateway da tabela link2
ip route add default proto static via $LINK2_GW src $LINK2_IP table link2
#
# Crio a regra de roteamento para cada tabela de acordo com a marcaç do pacote
#
# pacotes smtp que entraram pela tabela link1
ip rule add fwmark 1 from 192.168.1.3 table link1 prio 19
#
# pacotes smtp que entraram pela tabela link2
ip rule add fwmark 2 from 192.168.1.3 table link2 prio 20
#
# pacotes pop3 que entraram pela tabela link1
ip rule add fwmark 3 from 192.168.1.3 table link1 prio 21
#
# pacotes pop3 que entraram pela tabela link2
ip rule add fwmark 4 from 192.168.1.3 table link2 prio 22
#
# pacotes web que entraram pela tabela link1
ip rule add fwmark 5 from 192.168.1.4 table link1 prio 23
#
# pacotes web que entraram pela tabela link2
ip rule add fwmark 6 from 192.168.1.4 table link2 prio 24
#
# pacotes rdp que entraram pela tabela link1
ip rule add fwmark 7 from 192.168.1.4 table link1 prio 25
#
# pacotes rdp que entraram pela tabela link2
ip rule add fwmark 8 from 192.168.1.4 table link2 prio 26
#
# Caso vocêueira que o resto da rede interna se comunique com a internet pela
# tabela link1
ip rule add prio 30 table link1
#
# Atualizando o cache de roteamento
ip route flush cache
voce pode me ajudar?
Muito bom o artigo, me ajudou na solução de ter um DVR atrás de dois links passando por um servidor Linux. Como sempre vemos os artigos sobre dois links pensamos que o processo só vale para saída, mas o conhecimento acima funciona bem também como entrada.
Patrocínio
Destaques
Artigos
Vale a pena ter mais de uma interface grafica no seu Linux?
Estrutura e Funcionamento de um Ebuild no Gentoo Linux
Instalação e Configuração do Void com Cinnamon
Dicas
Montagem pré automática de HD externo usb em NTFS não funciona no Debian Trixie - Solução
Guia de instalação do Gentoo Linux com Cinnamon (UEFI, LUKS2, Btrfs)
Tópicos
No Ubuntu 26.04, sudo passou a mostrar os asteriscos ao digitar por pa... (0)
Criei um app de escrita acadêmica para brasileiros! (4)
Top 10 do mês
-

Xerxes
1° lugar - 130.036 pts -

Fábio Berbert de Paula
2° lugar - 64.714 pts -

Buckminster
3° lugar - 41.403 pts -

Alberto Federman Neto.
4° lugar - 33.031 pts -

Alessandro de Oliveira Faria (A.K.A. CABELO)
5° lugar - 22.628 pts -

edps
6° lugar - 21.684 pts -

Daniel Lara Souza
7° lugar - 21.236 pts -

Mauricio Ferrari (LinuxProativo)
8° lugar - 19.840 pts -

Sidnei Serra
9° lugar - 17.683 pts -

Andre (pinduvoz)
10° lugar - 15.866 pts